An increasingly significant part of a company's profitability now depends on how well its supply chain functions. This is why and how you can avoid a breakdown.

Supply Chain Risk Management has become ever more important over the last decade. 22% of companies hardly worried about it in 2005. Now only 9% say this. However, the risks identified at supplier level are numerous and include production capacity, logistics management and even management risk (in particular financial health).
Low cost options can prove expensive
When a purchasing department looks at a supplier's offer, they tend to focus on price and product availability while underestimating the importance of the location and insurance cover of these products. This desire to optimise costs in going for the low-cost option can prove expensive, especially in countries affected by natural disasters, health risks and geopolitical issues.
In 2015, Schneider Electric learned this to their cost in the Philippines. Although the group identified typhoons as the major risk, it was a 'simple' fire at a storage and packing warehouse that awakened the group to the risks. The consequence was a Supply Chain breakdown that was initially estimated to cost several million euros, although it ended up costing 'only' EUR 500,000.
Another more recent example is that of an oil company, which had previously been very cautious regarding insurance cover for its freight, but which lost EUR 800,000 following a fire in a cargo shipment on its way to Moscow. To make matters worse, another cargo shipment caught fire one month later leading to new losses of EUR 150,000.
Moving towards co-insurance
Although there is no longer any doubt that there is a real need, the insurance market is adopting a wait-and-see approach on the grounds that the guarantee is worrying insurers. They fear that during negotiations with the insured parties on the day of the claim, it will prove difficult to identify whether it relates to business risk or not. To avoid this issue of uncertainty, one of the solutions consists in making the client company the 'co-insurer' (between 60 and 90%).
Two types of cover are becoming more and more common: firstly, insuring against all risks, and secondly, insuring all the suppliers. In the first case, ‘all risks except’ insurance is now provided covering on average up to EUR 100 million (Europe and USA). Demand looks set to increase. For supplier cover, some companies stand out by offering cover of up to EUR one billion with sublimits for suppliers with a quality rank of 'N'.
10.06.2024
Electronic invoicing between companies to become mandatory
The bill to introduce this obligation in Belgium has been submitted to the Federal Parliament. If the draft bill is approved, B2B e-invoicing will become mandatory from 1 January 2026. Our experts explain why Belgium wants to introduce these new rules, what the implications are for your company and how we can better support you.
“The bill is consistent with international developments and initiatives at the European level,” says Nicolas De Vijlder, Head of Beyond Banking at BNP Paribas Fortis. "Europe's ambition is a harmonised digital standard. Structured e-invoicing between companies will also reduce the administrative burden of invoicing, enabling companies to work more efficiently and increase their competitiveness. The automation of VAT declarations will also help governments prevent tax fraud and adjust economic policies based on more qualitative data.”
Evolution rather than a revolution
“The new legislation is an evolution rather than a revolution,” adds Erik Breugelmans, Deputy Managing Director at BNP Paribas Factoring Northern Europe. "Digitalisation is becoming pervasive at all levels of society, as we have seen with the increase in electronic payments, as well as the additional obligations in recent years regarding electronic invoicing to the government. In this sense, the bill for mandatory electronic invoicing between companies is a logical next step. Our bank is happy to contribute to this process, although we do not intend to offer the same services as accounting software or fintechs. However, we are happy to help our customers with payments and financing."
The impact on businesses
“Customers need to be aware that the new regulations will have an impact on their internal and external processes,” continues Erik Breugelmans. "The majority of Belgian companies mainly serve an international market, which means that the introduction of electronic invoicing will be more complex for them than for companies operating in the domestic market. As the legislation will be introduced in one go, they need to start preparing now."
“The new rules will affect a company’s accounting department as well as its IT department,” emphasises Nicolas De Vijlder. "The procedural requirements are key, otherwise the automated process will not work. However, one of the main benefits of advanced automation is that everything can be done faster and more efficiently. The time between sending an invoice and paying it will be shorter and cash flows more predictable. In addition, it will also reduce the risk of error and fraud, as all transactions will pass through a secure channel."
Ready to offer you even more and better support
“Thanks to the far-reaching digitisation resulting from the new regulations, we will be able to further optimise payments,” concludes Erik Breugelmans. "As a bank, we need to finance our customers’ receivables as quickly and efficiently as possible, so that they have easier access to their working capital. In addition, because we have already gone through an entire process in terms of large-scale automation, we will be able to adapt quickly to the new rules. We can also draw on the expertise of the BNP Paribas Group, which is currently developing an e-invoicing solution for large companies."
Want to know more?
Listen to the episode on B2B e-invoicing :
08.03.2024
Has your company also locked in its energy prices?
The price of energy has experienced both high highs and low lows in recent years. This yo-yo behaviour is a worry to many entrepreneurs. Once again, BNP Paribas Fortis is here to offer you stability.

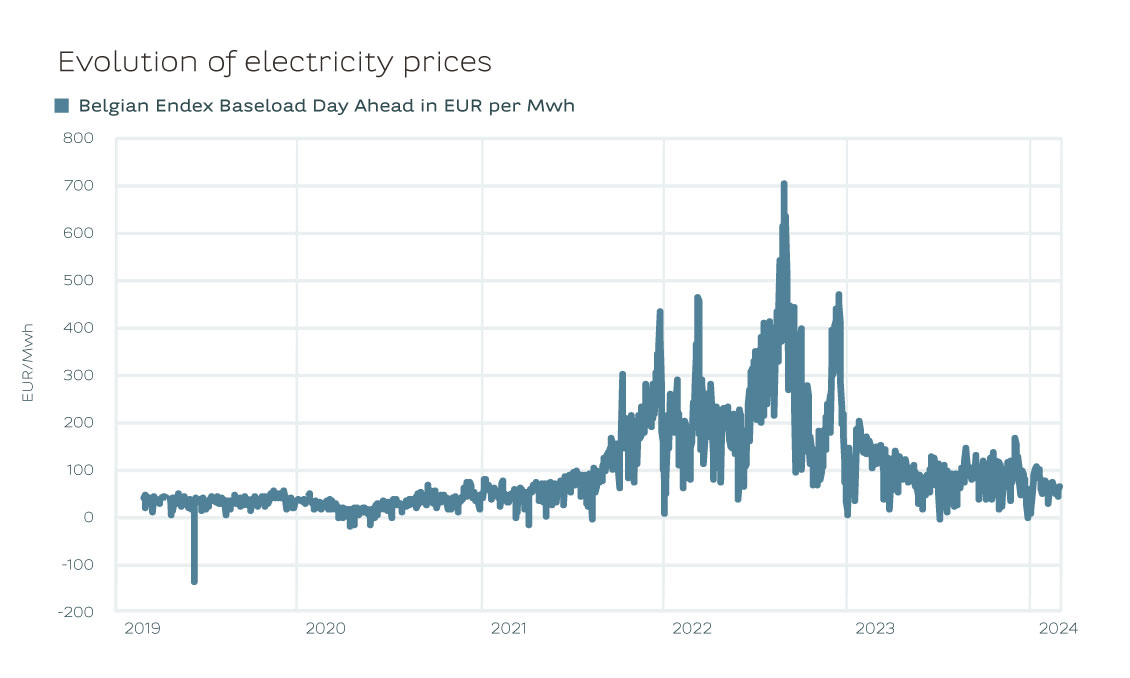
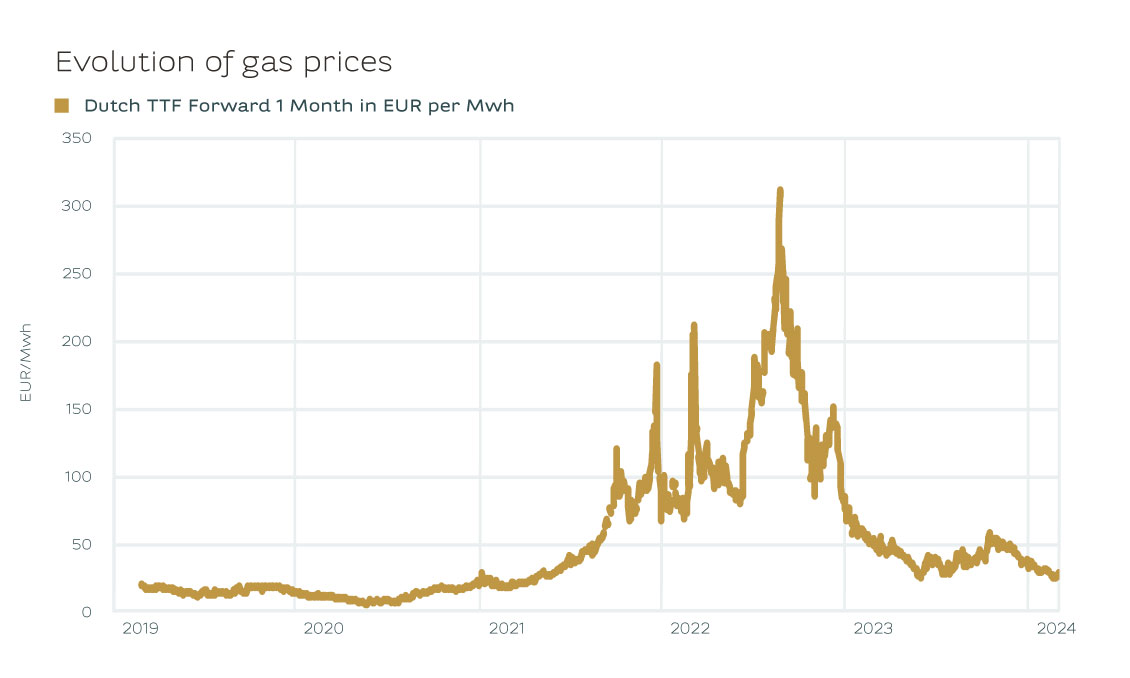
Controlling the price of energy: it’s an issue that’s almost impossible to avoid, or one that has been a recurring concern in your company over the past few years? We come from a time when energy prices were very volatile, with both high highs and low lows. These fluctuations have worried many entrepreneurs and, in some cases, caused huge additional costs. There is, however, a less well-known way for entrepreneurs to carry out risk management in this area. BNP Paribas Fortis is here to advise you.
Pendulum movement
Energy prices have been on a volatile ride in recent years. After the invasion of Ukraine, they rose to unprecedented levels. Gas prices rose to EUR 300 per MWh, while in previous years they had been around EUR 10-15 per MWh. Electricity prices rose to over EUR 600 per MWh. In previous years, the price was barely EUR 50 per MWh.
Crisis management
"As a result, BNP Paribas Fortis has received an increasing number of enquiries in recent years from companies looking to financially lock in their energy prices. Typically as a company you pay a variable price to the energy supplier. While you fix the price with the bank via a financial swap. Such financial swaps are also used to hedge other commodities (metals, oil products, etc.)."
Mattias Demets, Commodity Derivatives Sales at BNP Paribas Fortis
The energy crisis of 2022 sent shock waves through the economy. Especially in energy-intensive sectors such as metallurgy or chemicals, it became clear how much affordable energy was crucial to the survival of many companies. Those that were self-sufficient in their energy needs weathered the storm better than others. The energy crisis also highlighted the importance of risk management. Companies wanted, as the legislator put it, to act like "prudent and reasonable persons" - the former "good householder principle". They fixed their energy prices and came out of the crisis virtually unscathed. While others could only hope that energy prices would come down again.
'Never waste a good crisis' is a regularly heard truism. For this energy crisis, we can use this expression once again. It’s fascinating to see companies now taking charge of their own energy supply. The rise of PPAs – Power Purchase Agreements – is particularly remarkable. A PPA is an electricity purchase agreement between a power producer and a customer.
Risk management
Companies are also making great strides in risk management. In the past, it was often up to management to lock in energy prices. They saw it as an additional responsibility to negotiate with energy suppliers. But since the energy crisis, we have seen companies become much more professional. Managing energy prices is today a job in itself. Companies are increasingly thinking about the right strategy to manage their energy costs so that their energy prices come down. How and when they lock in energy prices has become more of an informed decision than ever before, allowing them to protect their margins in the event of rising prices.
As a result, BNP Paribas Fortis has received an increasing number of enquiries in recent years from companies looking to financially lock in their energy prices. Typically as a company you pay a variable price to the energy supplier. While you fix the price with the bank via a financial swap. Such financial swaps are also used to hedge other commodities (metals, oil products, etc.). A financial swap may seem a bit complex at first, but it’s actually not such an intricate transaction. Of course, other structures are also available, depending on your needs.
This is where the “prudent and reasonable person” returns to assess what lies ahead. After all, whether you’re looking for smart investment opportunities or advice on ways to control your energy costs, it ultimately boils down to two sides of the same coin. BNP Paribas Fortis not only thinks about investing with you as an entrepreneur, but also about ways to help you smartly and safely manage important expenses such as energy costs.
Permanent drop?
Regardless of how companies choose to fix their energy prices, the current market context is very interesting at the moment. Industry in Europe is going through tough times. Nevertheless, the economy is experiencing a soft landing – a slowdown, without a real recession. This is currently leading to lower gas and electricity prices. We have also had a mild and windy autumn and winter. As a result, energy producers have generated a historically high amount of electricity from renewable sources in recent months.
And there’s nothing to suggest that prices won't continue to fall. Europe is importing more LNG from the United States than ever before. Indeed, both the price of US gas and the cost of transporting it have fallen dramatically in recent months. However, elections are coming up in more than 65% of the developed world, and the geopolitical situation (Ukraine, Israel, Taiwan) could again cause volatility.
Prudence
Gas and electricity prices have not been this low for two years and the market is currently stable. But the 2022 energy crisis has shown that we must always be on our guard. Locking in your energy price is not only the most cost-effective tactic, but it will also protect you, as a business owner in times of increasing volatility.
For more information, please contact your relationship manager.
30.09.2020
Where will your 'international' roadmap take you?
Assessment? Check! Your strategy? All mapped out. You've also already determined your target market. But you've still got some way to go before you can cross borders... Some 'required stops'.
You're fully convinced of the benefits of internationalisation by now. You see it as an important lever for the growth of your business. But it's a process that doesn't happen overnight and is the result of a long decision-making process. You've carried out a preliminary assessment of your options before venturing into foreign markets. A checklist and initial indispensable considerations, so to speak, to find out whether the project was worthwhile. You then considered the choice of the most appropriate strategy for your business... You considered direct solutions such as e-commerce or commercial distribution. Or perhaps more sustainable establishment models, such as opening a branch or subsidiary, implementing synergies through a joint venture or a merger acquisition. This decision is based on a thorough analysis of the situation specific to your organisation. This approach often requires meticulous guidance. You will have also determined your target market during this process, which is a very important step. Your project's success now depends on the implementation of an action plan. And this phase inevitably brings with its new considerations and decisions...
NO SUCH THING AS ONE SIZE FITS ALL
In any case, your plan depends on your internationalisation strategy. The launch of an e-commerce platform or the choice of an intermediary imposes different requirements – in terms of due diligence obligations, financial resources or the definition of the target market, for example – than a merger acquisition. What's more, every merger-acquisition process is unique. What does this mean? That each adventure requires a tailor-made approach that considers the specific characteristics of your company, your products or services, your sector, your competitors, your added value, and more. Furthermore, the mapping of your international growth will be highly influenced by the characteristics of the target market. No magic formula then? Correct, but we do point out some common 'required stops' that deserve your attention.
- Cultural codes and language
- Relationships with partners
- Corporate culture
- Consumer habits and expectations
- Do’s and don'ts
- Don't lose sight of the regulatory aspects: they're essential!
1. The 'local' considerations
France is not Belgium. And Belgium is not Germany and certainly not Japan or Brazil. Each country has specific characteristics that shouldn't be taken lightly. It's more than 'folklore'! These are real 'keys' that you must assess correctly in order to make a difference. Numerous (internationally renowned) companies have come to grief while trying to do this. It's another commercial reality that can have a major impact on your action plan:
Note that a product that is successful in the domestic market will be perceived differently elsewhere. It will prompt you to take certain preliminary actions: call in experts from the country in question, carry out a more in-depth market study, participate in more local trade fairs, etc.
2. Adaptation of your commercial range
An important reflection that causes you to reassess a series of parameters:
From a commercial point of view: do your products and services meet the target group's specific needs? Does your range satisfy the previously identified needs? Is it sufficiently appealing? How will you position yourself? Does the quality meet the local standards? And so on.
From a legal point of view: the key question is whether you comply with the local market's regulatory or administrative requirements. Do you need special certifications? Do you have to comply with specific technical obligations? And so on.
- Carryout a thorough risk analysis.
- Prepare a budget for your expansion project and ensure you work out several scenarios, because you can always come up against surprises. Consider the fiscal context and the local market's specifications (infrastructure costs, employment costs, etc.).
- Plan distribution and transport circuits.
- Prepare a detailed schedule for your project's roll-out.
You must answer these questions to determine whether your market access strategy is ready in all respects: marketing and communication, value proposition, distribution methods, logistics chains, payment methods, etc. Not to mention your pricing policy. It may show that you need to make some adjustments at the production, distribution or commercial level.
3. Choice of partner
This isn't an easy task. Whatever your internationalisation project, this point plays a key role. You therefore need to set very clear objectives, missions and criteria that will serve as a guide to identify, prequalify and select the best local partners. The risk – and therefore the importance – of this approach is even greater in the case of a merger acquisition. A long-lasting marriage that must not fail... You will therefore need resources and time to complete your due diligence process.
4. You still have a way to go...
The following steps are no less important. We can give you the following tips in the meantime:
23.09.2020
Internationalisation: which strategy should you apply?
Conquering international markets is an indispensable growth lever for companies. Such a project can take different forms or follow different paths: from e-commerce to mergers and acquisitions.

International expansion can be an important growth factor for your company and an undeniable source of opportunities – both commercially and in terms of innovation or resilience. After a complete assessment of your current situation, an inevitable question follows: which strategy should you apply to realise your project? There's no magic formula or mapped-out path: in reality, you often adopt a wide-ranging approach based on various strategies. Nevertheless, we do see some broad outlines. And each has its own strengths and limitations. Whatever you decide, your choice should fit into an overall thinking and be in line with the current situation and the future of your business. The objective? Increasing your chances of success and keeping the risks under control as much as possible.
1. Direct and indirect export
This is naturally one of the most widely used strategies for conquering foreign markets. You can sell your products abroad through one or more channels:
- E-commerce: E-commerce is a fast and accessible solution to get 'far' with limited resources. Internet sales have grown very strongly in recent years but have a significant impact on the logistical workload. This includes not only technology and conformity, but also the commercial aspect. You are far from your target market and must deal with competitors from all over the world, while the internet knows no borders – and that's both an asset and an obstacle.
- A local intermediary: A gamble without too many risks, because you make use of the power of local sales – your agent delivers the customer's orders locally and you transfer them. The only thing left to do is to decide how to distribute your products. In this regard, it's important that you make full use of your knowledge of the foreign market. Think, for example, of consumers' consumption habits and expectations. Although this approach does not require major investments (payments on commission), it isn't entirely without risk. The success of your project is entirely in the hands of your local contact, leaving you to count on that partner's reliability.
- Commercial distribution: A similar approach to conquering the international market. This strategy can be implemented quickly and is the result of cooperation with independent distributors who are based in your target area. They buy the goods and then sell them, enabling you to benefit from their expertise and network. Unlike the intermediary, this distributor takes several tasks off your hands (invoicing, collection, marketing costs or import costs). Choosing the right partners and determining the terms of the contract is no easy task. After all, your project's success depends on it...
- Transfer of patents or technology: This is a way to make your know-how or technology pay off, not your products. This transfer of skills gives a foreign entity the right to use your methods or innovation within the framework of a previously established contract (geographical area, duration, etc.). An opportunity to go international where you 'outsource' production, sales and distribution. Contract preparation is one of the stumbling blocks of this approach.
2. Local establishment
Another model for internationalisation is to establish your business abroad. This means that you go local: you establish your entire value chain in another country, or you produce, distribute or sell your products there yourself. This geographical approach necessarily requires greater investment, but it also gives you more clout. This approach is also a way of reinforcing your resilience: the financial and commercial risks, as well as the pressure on your value chain, are spread over several areas. Over the years, a more flexible approach has also been introduced, allowing companies to move more flexibly in line with the international situation. Various options are also available here:
- Subsidiary or branch: In both cases, it's a matter of establishing a firm and lasting foothold in the local market. However, the project requires a solid foundation and a long-term vision. You should also think carefully about the legal status: do you opt for a subsidiary or for a branch? Consequently, when making this decision, take into account various factors: the degree of autonomy, the desired degree of decentralisation or consultation, the legal and tax implications, whether or not to produce locally (to take advantage of cheaper raw materials, for example), the financial resources that you can mobilise, and so on. In any case, a perfect lever for applying the well-known formula 'think globally, act locally'.
- International joint venture: This principle is based on the creation of synergies. Your company joins a company that already has a local presence and both companies complement each other. Each company benefits from the other's strengths while sharing the activity's risks, control and common costs. Such a joint venture or partnership often requires a customised legal structure. As you can see, a joint venture is not an easy marriage. It's therefore crucial that you find the right partner and come to an agreement with them concerning each party's input and responsibilities.
- Merger or acquisition: This growth strategy offers a few advantages. What's the greatest advantage? A merger or acquisition is a method of consolidating and diversifying your business. It's also a 'quick' way to conquer a new market by exploiting the local company's competitive advantages (technological, commercial, etc.). Such a project naturally entails not only potential benefits, but also risks. For example, you may misjudge the sources of value creation or the risks, or have difficulty integrating.
As you can see, your international project's success depends on many factors. And, first and foremost, on your own strategic choices and your ability to develop a clear vision of exactly what you want to achieve. From the development of a commercial partner network to a sustainable local presence, there are many options that deserve not only thorough consideration, but also professional guidance.
Contact us
